German encrypted email service Tutanota suffers DDoS attacks
Security Affairs
SEPTEMBER 19, 2020
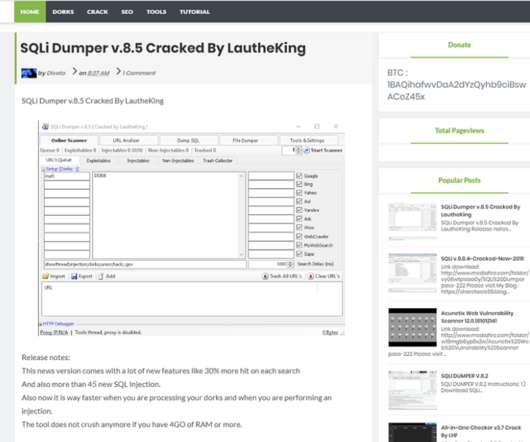
The popular encrypted email service Tutanota was hit with a series of DDoS attacks this week targeting its website fist and its DNS providers later. Encrypted email service, Tutanota suffered a series of DDoS attacks that initially targeted the website and later its DNS providers. ” continues the post.























Let's personalize your content