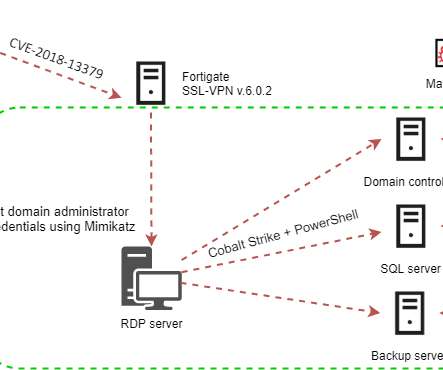
New Cring ransomware deployed targeting unpatched Fortinet VPN devices
Security Affairs
APRIL 7, 2021
Attackers are actively exploiting the CVE-2018-13379 flaw in Fortinet VPN to deploy the Cring ransomware to organizations in the industrial sector. Upon compromising the domain administrator account, threat actors could distributee malware to other systems on the same network. ” continues Kaspersky.















Let's personalize your content