A Deep Dive on the Recent Widespread DNS Hijacking Attacks
Krebs on Security
FEBRUARY 18, 2019
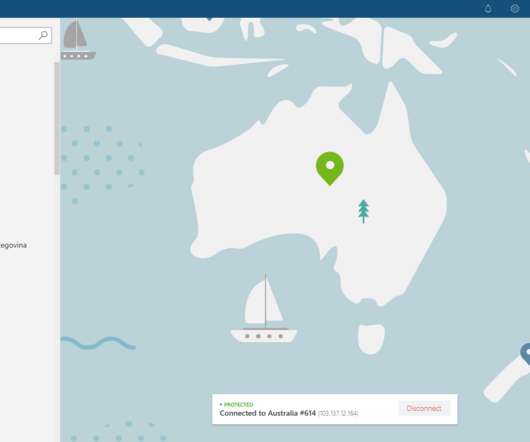
27, 2018, Cisco’s Talos research division published a write-up outlining the contours of a sophisticated cyber espionage campaign it dubbed “ DNSpionage.” Talos reported that these DNS hijacks also paved the way for the attackers to obtain SSL encryption certificates for the targeted domains (e.g. PASSIVE DNS.

















Let's personalize your content