8Base ransomware operators use a new variant of the Phobos ransomware
Security Affairs
NOVEMBER 19, 2023
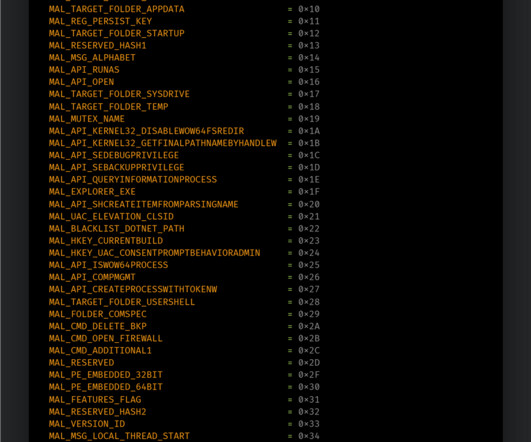
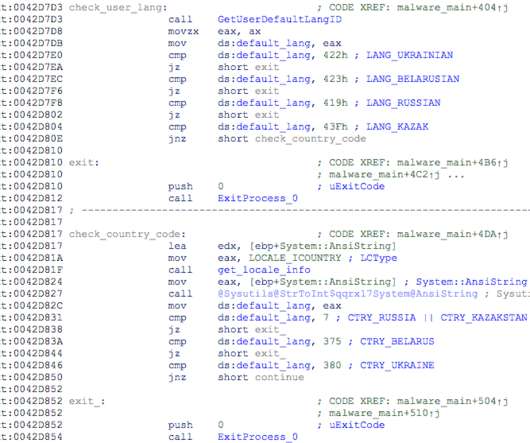
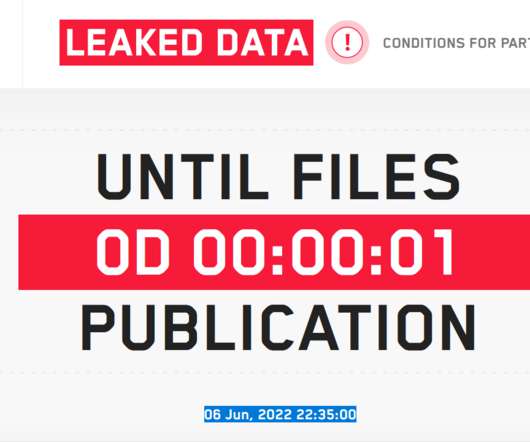
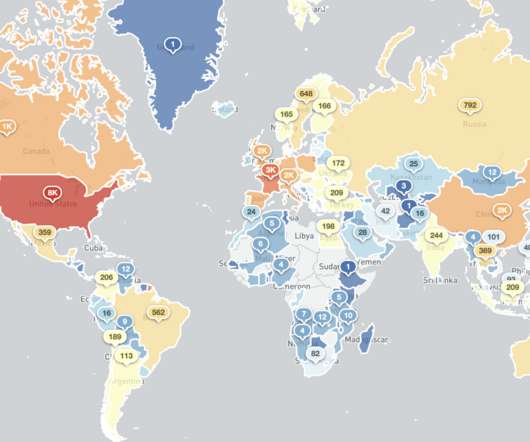
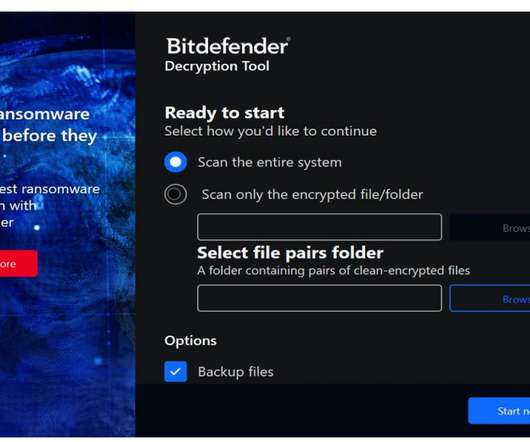
8Base ransomware operators were observed using a variant of the Phobos ransomware in a recent wave of attacks. Cisco Talos researchers observed 8Base ransomware operators using a variant of the Phobos ransomware in recent attacks. The ransomware component is then decrypted and loaded into the SmokeLoader process’ memory.









































Let's personalize your content