How to Stop Phishing Attacks with Protective DNS
Security Boulevard
OCTOBER 2, 2023
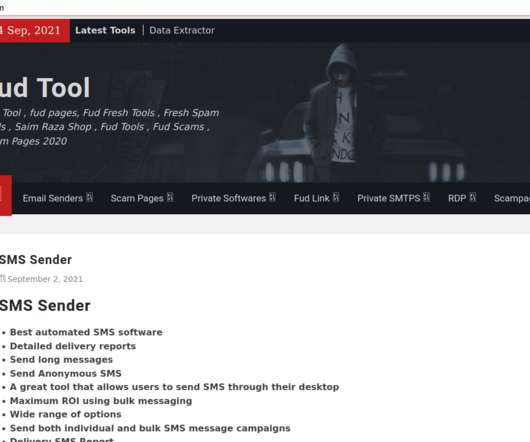
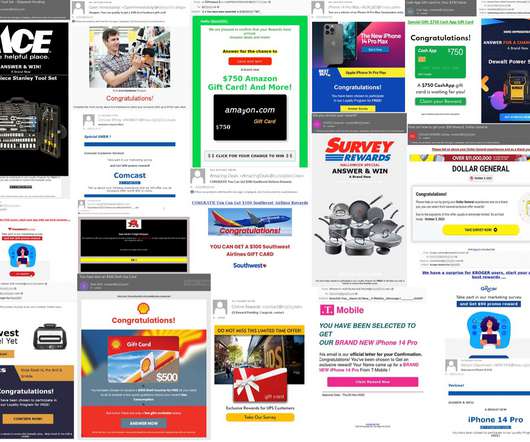
Phishing Threats Are Increasing in Scale and Sophistication Phishing remains one of the most dangerous and widespread cybersecurity threats. Phishing is now the most common initial attack vector, overtaking stolen or compromised credentials. Phishing attacks are becoming more difficult to detect. billion USD globally.
























Let's personalize your content