Top 10 web application vulnerabilities in 2021–2023
SecureList
MARCH 12, 2024
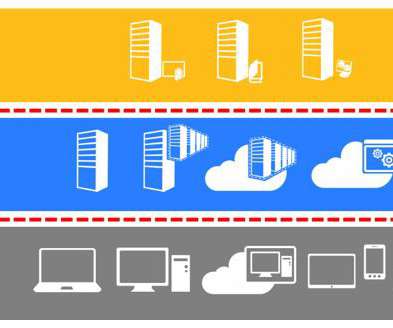
More than a third (39%) used the microservice architecture. Compared to Broken Access Control, Sensitive Data Exposure contained a greater number of low-risk vulnerabilities, but high-risk ones were present as well. Server-Side Request Forgery (SSRF) The popularity of the cloud and microservice architectures is on the rise.
















Let's personalize your content