YouTube creators’ accounts hijacked with cookie-stealing malware
Security Affairs
OCTOBER 20, 2021
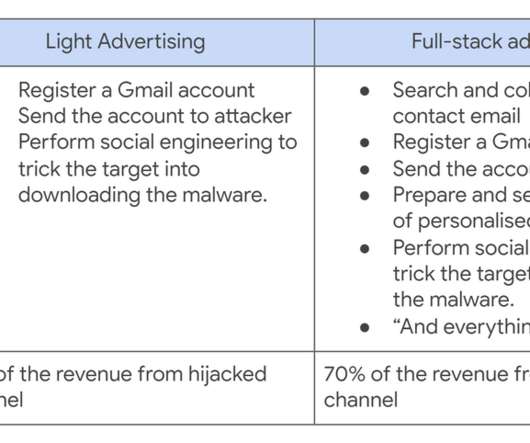
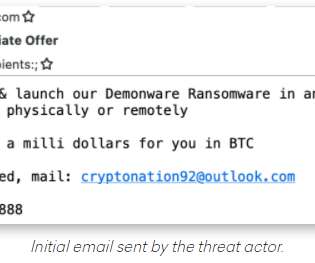
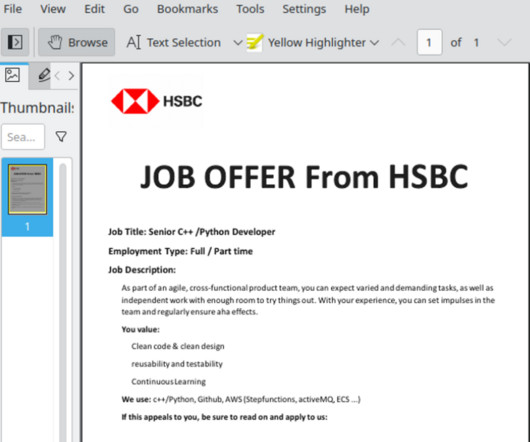
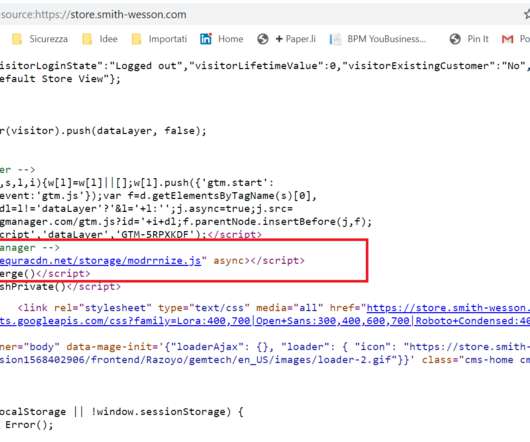
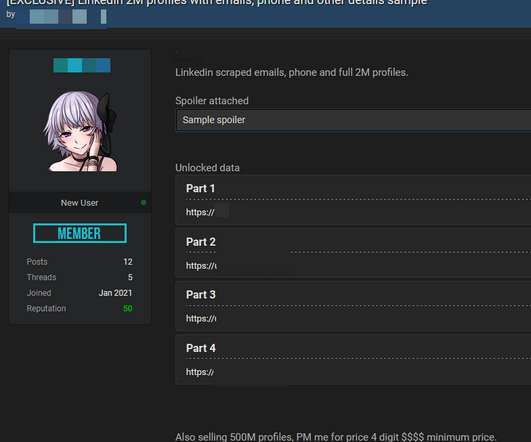
The malware landing page is disguised as a software download URL that was sent via email or a PDF on Google Drive, or via Google documents containing the phishing links. The researchers identified around 15,000 actor accounts, most of which were created for this campaign. ” reads the analysis published by Google TAG.









































Let's personalize your content