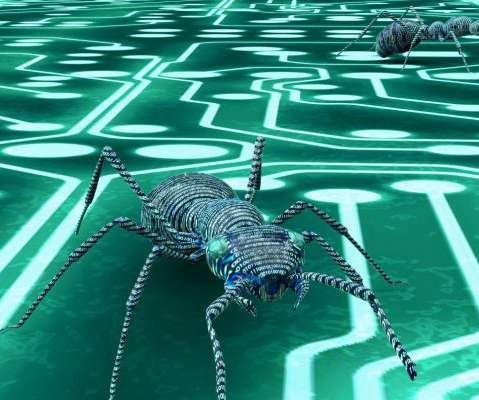
Types of Malware & Best Malware Protection Practices
eSecurity Planet
FEBRUARY 16, 2021
Jump ahead: Adware. Adware, also known as malvertising , is a type of malware that downloads or displays advertisements to the user interface. Rather than stealing data, adware is more of an irritant forcing users to see unwanted ads. Most users are familiar with adware in the form of unclosable browser pop-ups.













Let's personalize your content