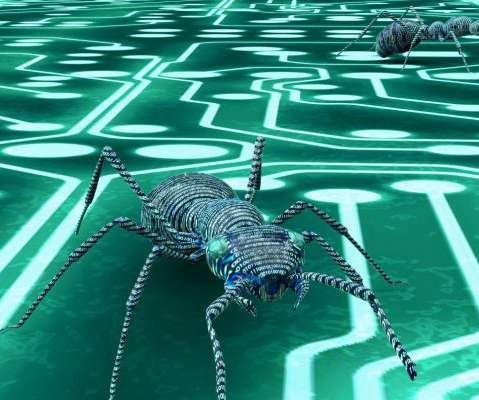
What is Malware?
Identity IQ
APRIL 29, 2021
Gaining control of multiple computers to launch denial-of-service (DDoS) attacks against other networks. Viruses can lead to deleted or encrypted files, modified applications, or system malfunctions. Adware is software designed to serve advertisements to you, either within your web browser or in other programs. Ransomware.


















Let's personalize your content