Malvertising Is a Cybercrime Heavyweight, Not an Underdog
SecureWorld News
MARCH 29, 2024
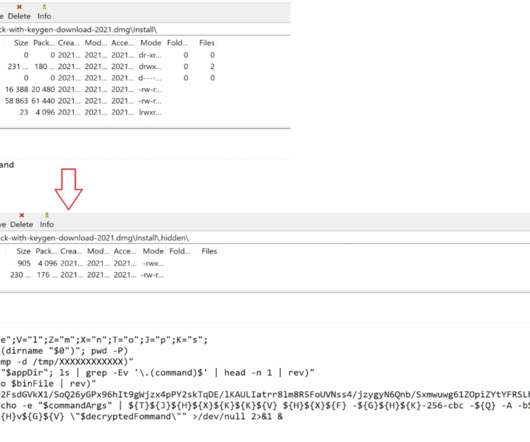
Malvertising acts as a vessel for malware propagation. Scammers and malware operators are increasingly adept at mimicking popular brands in their ad snippets, which makes it problematic for the average user to tell the wheat from the chaff. One of the biggest pitfalls with malvertising is how difficult it can be to detect.














Let's personalize your content