HYAS Protection for growing businesses
Security Boulevard
JUNE 22, 2023
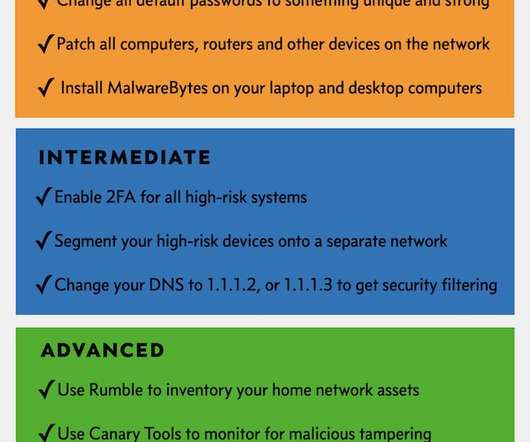
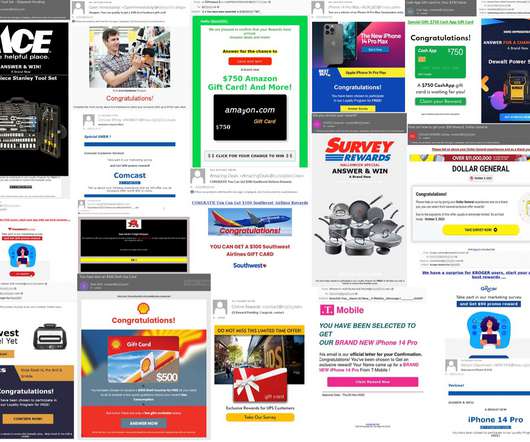
Securing SMB Success: The Indispensable Role of Protective DNS Cyber attacks pose as much risk to small and medium-sized businesses (SMBs) as they do to large organizations — if not more. Implementing a Domain Name Service (DNS) security solution is the most efficient way to protect your business against a wide variety of attacks.






















Let's personalize your content