Defeating Malvertising-Based Phishing Attacks
Security Boulevard
MARCH 3, 2023
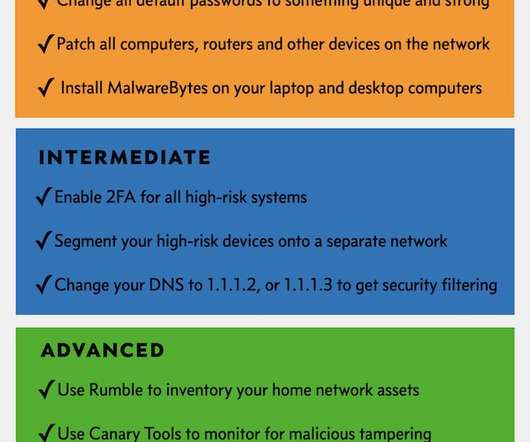
Malvertising Enters a New Age While Google grapples with the potential threat that ChatGPT poses to its advertising business, cybercriminals are taking advantage of Google Ads to ramp up their phishing attacks on unsuspecting victims. Your firewall had no problems letting the requested HTTPS traffic through. Next-gen protective DNS.























Let's personalize your content