Solving Identity Theft Problems: 5 Actionable Tips
CyberSecurity Insiders
NOVEMBER 14, 2021
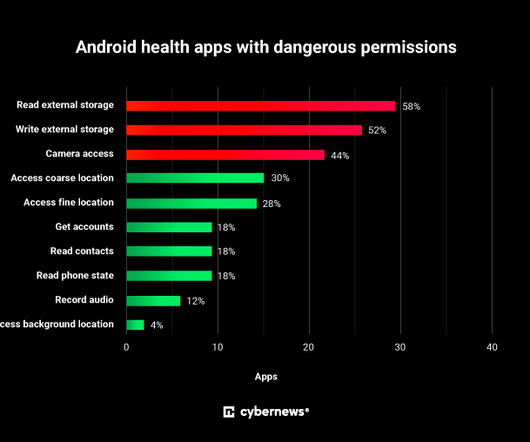
Identity theft (or ID theft) is not a new problem, but in today’s well-connected society it is a problem that grows at an incredible rate. . Put in a few words, ID theft is when someone pretends to be someone else, using their credentials and taking various actions in their name. 2: Use Strong Passwords.




















Let's personalize your content