‘Tis the season for protecting your devices with Webroot antivirus
Webroot
NOVEMBER 23, 2021
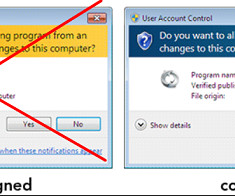
Whether you purchase a new device or receive one as a gift, now is the time to consider the importance of protecting it with an antivirus program. What is antivirus? Antivirus programs accomplish this by conducting behavior-based detection, scans, virus quarantine and removal. Do I really need antivirus? In a word, yes.













Let's personalize your content