CrowdStrike 2025 Global Threat Report: 51-Second Breaches Shake Cybercrime
eSecurity Planet
MARCH 3, 2025
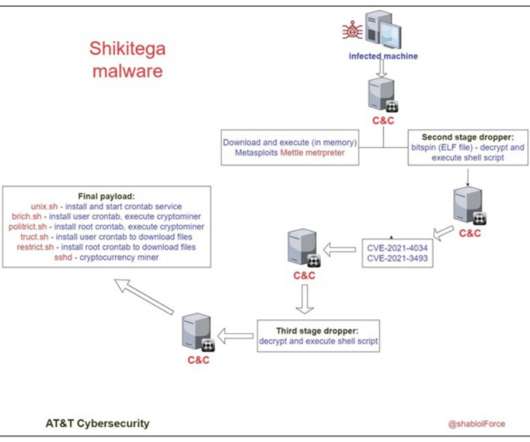
In a comprehensive new report, cybersecurity leader CrowdStrike unveiled a rapidly evolving threat landscape that challenges traditional defenses. Unprecedented speed and scale of attacks The report reveals that some cyberattacks break out within 51 seconds, with an average breach time of 48 minutes.






















Let's personalize your content