Cyber Insurers Pull Back Amid Increase in Cyber Attacks, Costs
eSecurity Planet
MAY 27, 2021
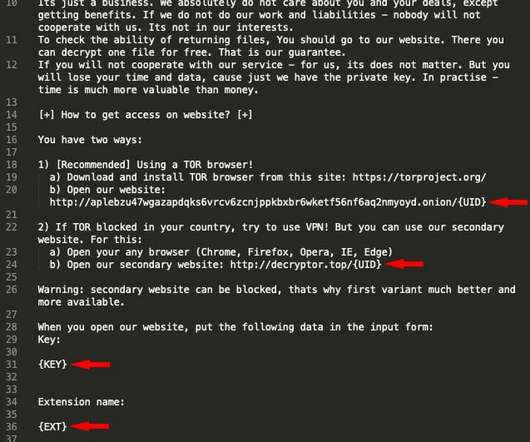
The explosion of ransomware and similar cyber incidents along with rising associated costs is convincing a growing number of insurance companies to raise the premiums on their cyber insurance policies or reduce coverage, moves that could further squeeze organizations under siege from hackers. Insurers Assessing Risks.



































Let's personalize your content