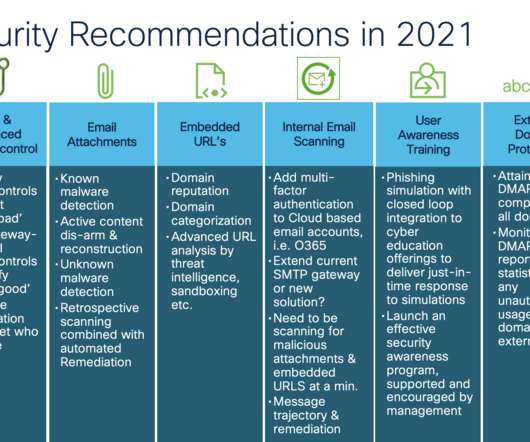
Email Security Recommendations You Should Consider from 2021
Cisco Security
AUGUST 17, 2021
Now mix in architectural changes that support cloud productivity suites like Microsoft 365 and Google’s G-Suite to accelerate your business to cloud-based email security services. When it comes to safeguarding email against today’s advanced threats like phishing and malware information is power.





























Let's personalize your content