NDR unveiled as essential when complying with the Executive Order
Cisco Security
NOVEMBER 18, 2021
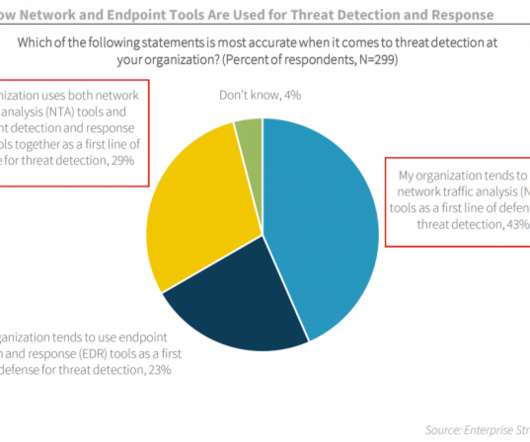
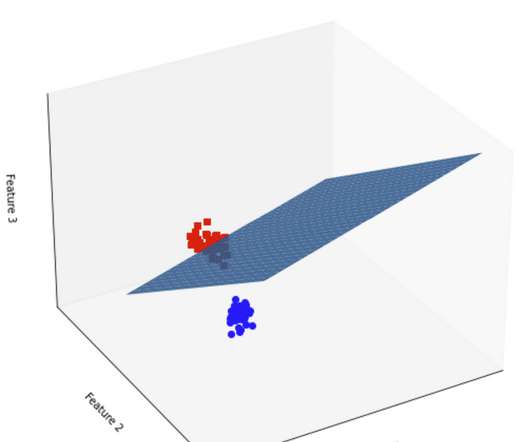
Also cited is the directive to follow the National Institute of Standards and Technology (NIST) guidance when modernizing networks within a zero-trust architecture (see NIST Special Publication 800-207 ). While the term NDR is relatively new, the technology is not. See figure 1]. Detection of stealthy and unknown threats.














Let's personalize your content