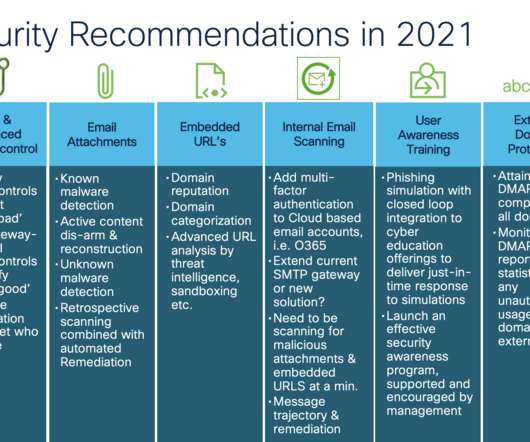
Email Security Recommendations You Should Consider from 2021
Cisco Security
AUGUST 17, 2021
Here is a brief review of the 2021 Email Security Recommendations: Spam and Unwanted Email Detection: For most organizations, spam & unwanted email volumes are running in the low 80% of their entire email volume. Traditional technologies here work by detecting the known malicious email, attempted spoofing attempts, and so on.




















Let's personalize your content