Establishing an IAM Blueprint for Securing Manufacturing Environments
Thales Cloud Protection & Licensing
JULY 26, 2022
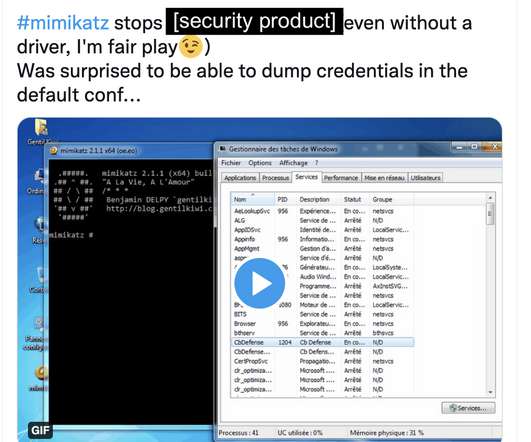
The convergence of IT and OT domains has emerged another infection vector – weak access controls to authenticate employees into a wide range of cloud-based and on-premises systems. A cornerstone to protecting this hybrid environment is building strong access controls with appropriate multifactor authentication methods.












Let's personalize your content