Multi-Factor is incomplete without backup codes
CyberSecurity Insiders
JANUARY 10, 2022
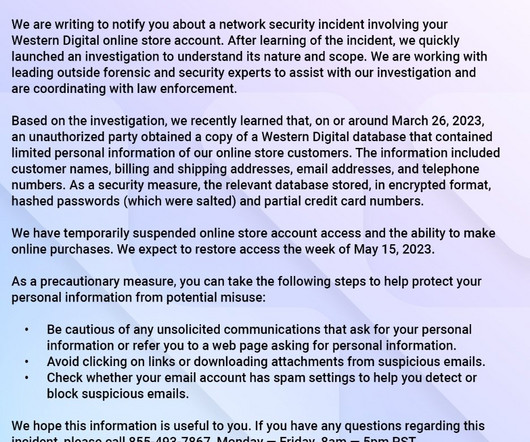
This blog was written by an independent guest blogger. This created an unusual conundrum, whereas, not only does my phone contain the authenticator application, but the only backup method the site offers is to send a text message to a registered phone number if the authenticator application is unavailable. Happy shopping!








































Let's personalize your content