The Link Between Ransomware and Cryptocurrency
eSecurity Planet
DECEMBER 21, 2021
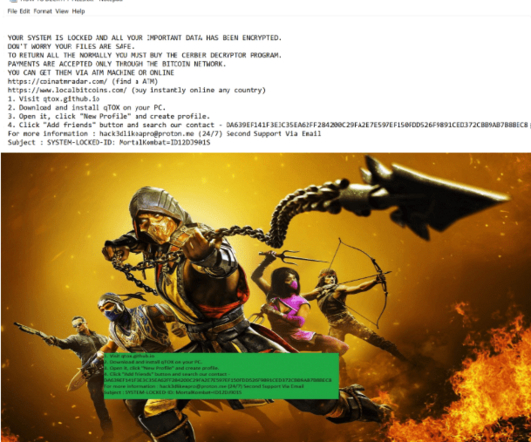
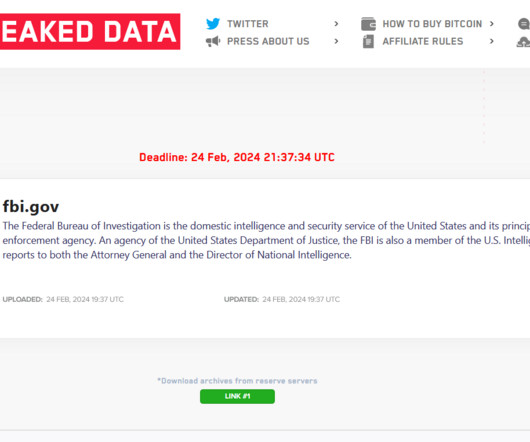
Cryptocurrency Fuels Ransomware. One constant in all this will be cryptocurrency, the coin of the realm when it comes to ransomware. Cryptocurrency really is fueling this in a sense. … If you were to take cryptocurrency away from that, they don’t have a convenient digital platform.






























Let's personalize your content