How to protect backup servers from ransomware
CyberSecurity Insiders
FEBRUARY 16, 2023
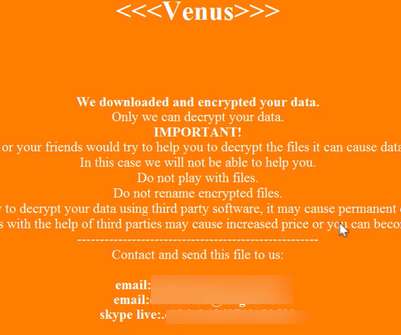
We all know that backup servers are only the sole saviors to an organization when a ransomware incident strikes their IT infrastructure. Blocking a backup server from Lightweight directory access protocol (LDAP) also makes sense as it blocks hackers from accessing usernames and passwords fraudulently.











































Let's personalize your content