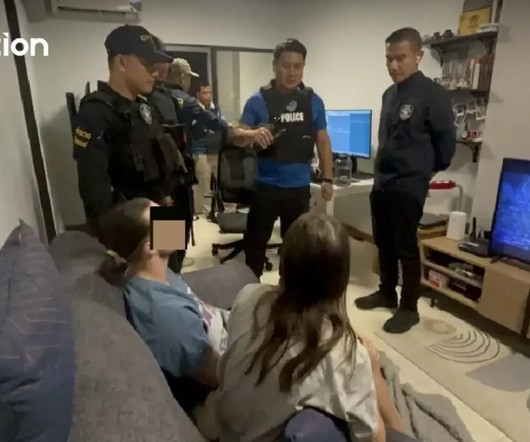
Exposed eyes: 40,000 security cameras vulnerable to remote hacking
Security Affairs
JUNE 12, 2025
Over 40,000 internet-exposed security cameras worldwide are vulnerable to remote hacking, posing serious privacy and security risks. Bitsight warns that over 40,000 security cameras worldwide are exposed to remote hacking due to unsecured HTTP or RTSP (Real-Time Streaming Protocol) access.













Let's personalize your content