Fake Lawsuit Threat Exposes Privnote Phishing Sites
Krebs on Security
APRIL 4, 2024
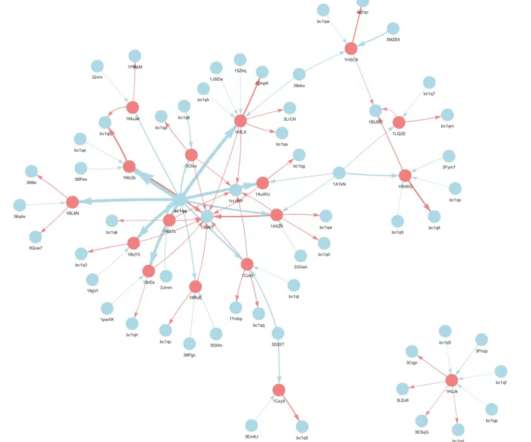
The disclosure revealed a profitable network of phishing sites that behave and look like the real Privnote, except that any messages containing cryptocurrency addresses will be automatically altered to include a different payment address controlled by the scammers. co showing the site did indeed swap out any cryptocurrency addresses.



















Let's personalize your content