Cybersecurity’s Comfort Zone Problem: Are you Guilty of it?
Jane Frankland
APRIL 15, 2025
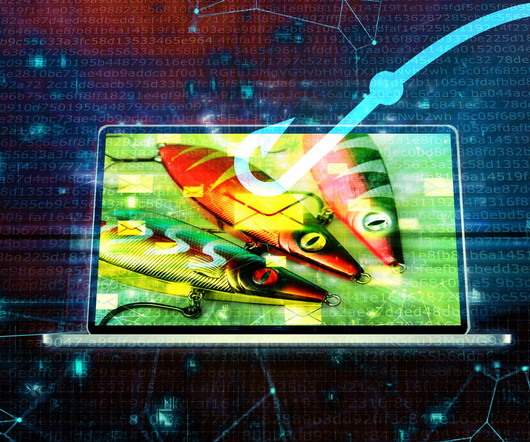
Instead of focusing on accessible, impactful solutions like human risk management, we gravitate toward shiny new technologiestools and systems that feel exciting, measurable, and comfortably within our domain of expertise. The hard truth is that technology alone cant fix the root causes of cyber risk.















































Let's personalize your content