Thales 2023 Data Threat Report: The Increased Telco Cybersecurity Challenges in the 5G Era
Thales Cloud Protection & Licensing
SEPTEMBER 11, 2023
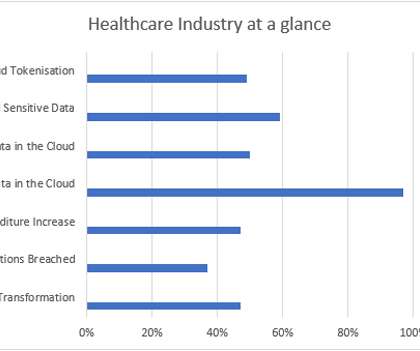
Thales 2023 Data Threat Report: The Increased Telco Cybersecurity Challenges in the 5G Era madhav Tue, 09/12/2023 - 05:15 Telecommunications firms have always faced a unique set of security challenges. IoT devices have a history of being the targets of botnet recruitment and engines for distributed denial of service (DDoS) attacks.




























Let's personalize your content