How Do You Quantify Risk? Best Techniques
Centraleyes
FEBRUARY 13, 2024
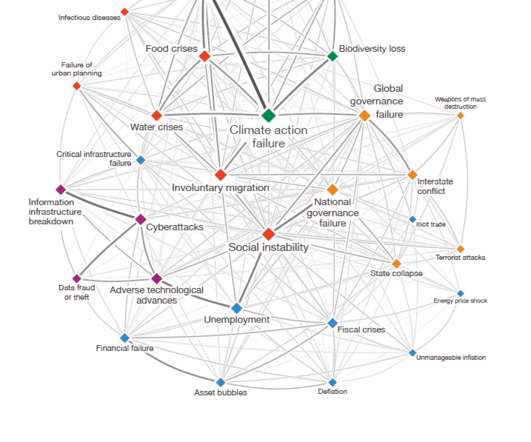
Categorizing risks as high, medium, or low has been the go-to method for organizations seeking to prioritize their cybersecurity efforts. Ten Risks in a Bed Remember the nursery rhyme? Enter the need for a more precise and actionable approach — Cyber Risk Quantification. What is Cyber Risk Quantification?























Let's personalize your content