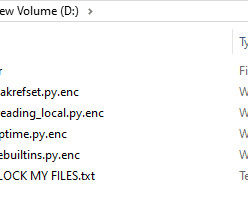
The Stealthy Rise of Python Scripted Ransomware Attacks
Penetration Testing
JANUARY 31, 2024
In the Internet age, where cyber threats continually evolve, the rise of scripted ransomware marks a new era of digital extortion.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Penetration Testing
JANUARY 31, 2024
In the Internet age, where cyber threats continually evolve, the rise of scripted ransomware marks a new era of digital extortion.

Penetration Testing
FEBRUARY 15, 2024
In the ever-evolving landscape of cyber threats, ransomware has emerged as one of the most pervasive and damaging forms of malware.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Penetration Testing
DECEMBER 5, 2023
As the digital landscape evolves, so does the nature of cyber threats. 2023 witnessed a significant shift in the tactics and approaches of cyber attackers, influenced by global conflicts and advancements in technology.

Penetration Testing
DECEMBER 4, 2023
Emerging from the shadows of Pyongyang, a North Korean hacking organization known as Andariel has been wreaking havoc in the digital realm, stealthily infiltrating South Korean firms and institutions, stealing sensitive data, and extorting... The post Andariel: North Korea’s Cyber Threat Actor Steals Data, Launches Ransomware Attacks (..)

Penetration Testing
DECEMBER 31, 2023
In a digital landscape where cyber threats are constantly evolving, Microsoft’s latest Threat Intelligence report, covering activity since mid-November 2023, sheds light on the sophisticated strategies employed by cybercriminals.

Penetration Testing
JANUARY 18, 2024
In recent years, cybersecurity has become a paramount concern, and it’s no surprise given the persistent and cunning nature of cyber threats.

Penetration Testing
JANUARY 16, 2024
In 2023, the world faced an unprecedented surge in cyber threats, a storm that Check Point Research’s analysis has vividly captured. The year marked a new high in cyber attacks, with a 1% increase... The post Ransomware Surge: 1 in 10 Organizations Targeted Globally in 2023 appeared first on Penetration Testing.

Penetration Testing
JANUARY 9, 2024
In the ever-evolving landscape of cyber threats, a new name has emerged with a notorious reputation – Pikabot.

Penetration Testing
NOVEMBER 1, 2023
In the ever-evolving landscape of cyber threats, a new alarm has been sounded for Apache ActiveMQ server administrators.

Penetration Testing
DECEMBER 3, 2023
In the ever-evolving landscape of cyber threats, a new formidable player has emerged: the Bluesky ransomware.

Penetration Testing
DECEMBER 3, 2023
The BlackBerry Global Threat Intelligence Report for November 2023 provides a deep dive into the current cybersecurity landscape, offering invaluable... The post Cybercrime Rampant: Novel Malware Attacks Triple in Frequency, BlackBerry Warns appeared first on Penetration Testing.

SecureWorld News
JUNE 13, 2023
The new Beep malware is top of mind for organizations and individuals. This pervasive threat is delivered via email attachments, Discord, and OneDrive URLs. State-sponsored cyber espionage is becoming increasingly common, with threat actors operating out of Russia, potentially India, and the Asia-Pacific (APAC) region.

Zigrin Security
OCTOBER 11, 2023
Let’s have a look at the types of threat actors and what type of data they would like to obtain. For a detailed threat actor description do not forget to check out our blog article about selecting between black-box, white-box, and grey-box penetration tests and also you would know which pentest you need against a specific threat actor.
Joseph Steinberg
JANUARY 22, 2024
In the Cybersecurity for Dummies section of the book, readers learn in simple, straightforward language about various cyber-threats that they face, and how to protect themselves against such threats – as well how to recover if they have already suffered a malware infection or data breach, or otherwise have had their cybersecurity undermined.

SecureWorld News
AUGUST 8, 2022
Cybersecurity and Infrastructure Security Agency (CISA) and the Australian Cyber Security Centre (ACSC) released a joint Cybersecurity Advisory (CSA) providing details on the top malware strains of 2021. The top malware strains in 2021 included remote access Trojans (RATs), banking Trojans, information stealers, and ransomware.

The Last Watchdog
JUNE 21, 2020
Ransomware is undoubtedly one of the most unnerving phenomena in the cyber threat landscape. Related: What local government can do to repel ransomware Ransomware came into existence in 1989 as a primitive program dubbed the AIDS Trojan that was spreading via 5.25-inch None of these early threats went pro.

Penetration Testing
DECEMBER 20, 2023
As we approach the end of 2023, it’s crucial to reflect on the cyber threats that have shaped our digital world.
eSecurity Planet
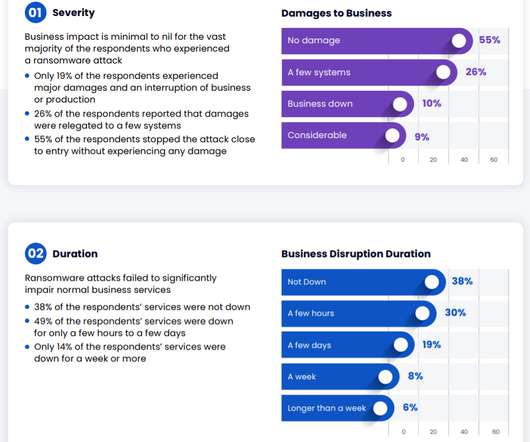
NOVEMBER 19, 2021
In a year in which ransomware attacks seem to get worse by the day, companies have made surprising progress defending themselves against attacks. Ransomware protection spending (source: Cymulate). Where the greatest optimism comes in is in what tends to happen when a company is hit with ransomware, according to the report.

CyberSecurity Insiders
OCTOBER 14, 2021
The FBI recently published a warning stating that ransomware gang OnePercent Group has been attacking companies in the US since November 2020. Ransomware is then downloaded and the breach is underway. Ransomware is then downloaded and the breach is underway. How to spot their scam and protect yourself.

Security Boulevard
DECEMBER 19, 2022
setting the foundations for successful targeted malware and exploits serving campaigns. Sample uses of these stolen and compromised databases includes: - setting the foundation for a successful spear-phishing campaigns. setting the foundations for successful widespread spam and botnet propagation campaigns.

McAfee
JUNE 17, 2021
Imagine if you had one place where you found a comprehensive real time security posture that tells you exactly where the looming current cyber risks are and the impact? Let’s consider a recent and relevant cyber threat. Ransomware doesn’t just cost money—or embarrassment—it can derail careers. Scoring Points at Work.
Security Boulevard
OCTOBER 2, 2023
Source: IBM Security: Cost of a Data Breach Report 2023) According to recent research, the number of phishing attacks vastly outpaces all other cyber threats. Malware payloads - Malicious attachments or links that install info-stealing malware, ransomware, or remote access Trojans via phishing messages.

CyberSecurity Insiders
SEPTEMBER 21, 2021
A clean machine – real simple: Keep all software on internet-connected devices – including personal computers, smartphones, and tablets – current to reduce the risk of infection from ransomware and malware. Penetration test results may help drive your security budget and prioritize spending.

CyberSecurity Insiders
JUNE 7, 2023
Cybercriminals take advantage of their weak security infrastructure and exploit the behavior of careless employees to launch insider threats and other cyber-attacks successfully. A report reveals various cyber-attacks that often target small businesses, such as malware, phishing, data breaches, and ransomware attacks.
SecureWorld News
MARCH 1, 2023
Hallmarks of a 'mental payload' that pulls the right strings Simply put, any phishing email aims to make a recipient slip up in one of the following two ways: clicking a malicious link or downloading a malware-riddled file. They add an extra layer of monetization to these attacks. This kind of foul play is known as spear-phishing.

CyberSecurity Insiders
JANUARY 18, 2022
The same symptoms will occur in your IT environment as the malware spreads downloading data and expanding across your global network corrupting backups and leaving little options. Ransomware and stolen customer data can put an enterprise out of business for months. Have a ransomware playbook in place and run preparedness drills.

Cytelligence
FEBRUARY 25, 2023
Cybersecurity refers to the set of technologies, processes, and practices designed to protect digital devices, networks, and data from cyber threats. With the increase in the number of cyber-attacks and data breaches, it has become essential to take cybersecurity seriously. It includes viruses, worms, and Trojans.

Spinone
DECEMBER 26, 2018
VoIP phishing and impersonation also victimized millions of corporate employees across the world , contributing to an even greater cyber threat. Cloud security success and choosing the right investments is all about having a clear understanding of threat types and their resulting damages.

Spinone
OCTOBER 27, 2020
Cyber threats exist in many different types and forms. Never before has it been more important for your business to give proper attention to cybersecurity threats and how your business can protect itself against them. What types of scans are performed during vulnerability testing? What is a cybersecurity risk assessment?

eSecurity Planet
JANUARY 27, 2022
As threats mount from ransomware gangs , Russian-backed hacker groups , and other nation-sponsored attackers and as the growth in remote work makes security management increasingly complicated, many companies are finding it makes sense to turn to a managed security service provider (MSSP) for help with handling an extremely complex threat landscape.

eSecurity Planet
APRIL 11, 2022
As technologies advance, and cyber threats with them, deception has become a big part of the 21st century cybersecurity battle. Deception tools can thus be an important defense against advanced persistent threats (APTs). Illusive has been attacked by more than 140 red teams and has never lost a penetration test.

eSecurity Planet
FEBRUARY 13, 2023
Web application scanners test your websites and web-facing apps for vulnerabilities. These tests typically use vulnerability scanners. Penetration testing is a similar approach, but typically involves teams of security pros attempting to simulate a cyber attack to identify weaknesses that could be exploited by hackers.

eSecurity Planet
MAY 19, 2023
It offers a wide range of security testing capabilities, including code scanning, vulnerability assessment , and penetration testing. It helps organizations ensure the security and compliance of their cloud-based applications, protecting sensitive data, preventing unauthorized access, and defending against threats.

ForAllSecure
FEBRUARY 23, 2021
Crawley: Pen testing is when you simulate cyber attacks, so you're not actually conducting cyber attacks because you have the consent of the owner of the network or the computer application that you're penetration testing, but within the rules that your client has given you. You are acting as your cyber attacker.

ForAllSecure
FEBRUARY 23, 2021
Crawley: Pen testing is when you simulate cyber attacks, so you're not actually conducting cyber attacks because you have the consent of the owner of the network or the computer application that you're penetration testing, but within the rules that your client has given you. You are acting as your cyber attacker.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content