Russian Phobos ransomware operator faces cybercrime charges
Security Affairs
NOVEMBER 19, 2024
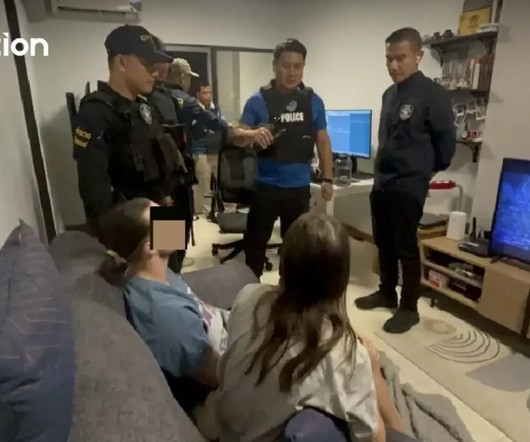
Russian Phobos ransomware operator Evgenii Ptitsyn, accused of managing attacks, was extradited from South Korea to the US to face cybercrime charges. Russian Phobos ransomware operator Evgenii Ptitsyn, suspected of playing a key role in the ransomware operations, was extradited from South Korea to the US to face cybercrime charges.










































Let's personalize your content