PRODUCT REVIEW: Nisos OSINT Monitoring and Analysis
CyberSecurity Insiders
OCTOBER 3, 2022
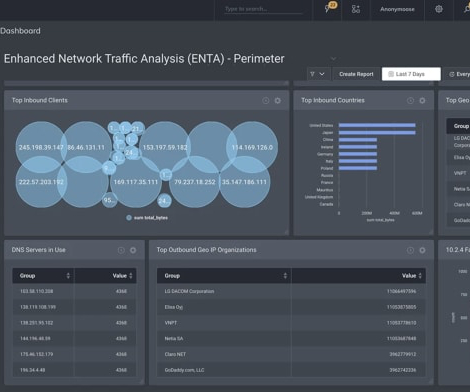
Monitoring and tracking potential threats from the dark web, open source, and social media platforms to detect threats that could attack your organization is critical to ensure public and corporate safety and security. While most intelligence vendors provide cyber threat data, few cover the breadth of disciplines of Nisos.





















Let's personalize your content