How to Think about Threat Detection in the Cloud
Anton on Security
MAY 19, 2022
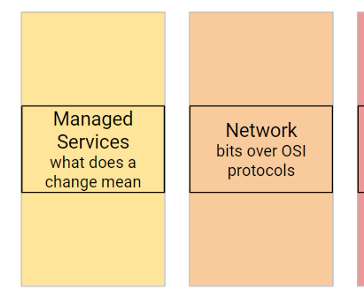
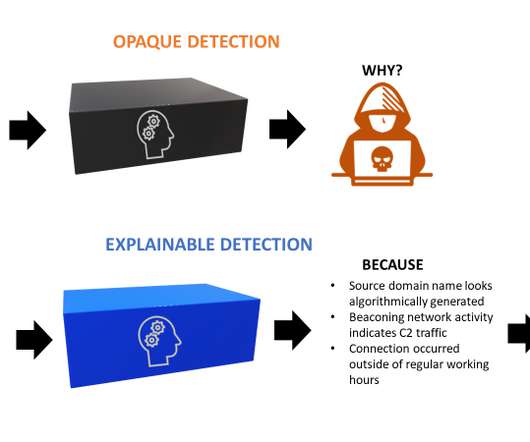
In this post, we will share our views on a foundational framework for thinking about threat detection in public cloud computing. To start, let’s remind our audience what we mean by threat detection and detection and response. All these affect how we are doing threat detection for the cloud environment.















































Let's personalize your content