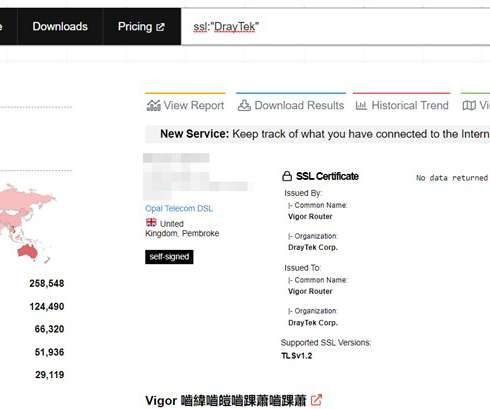
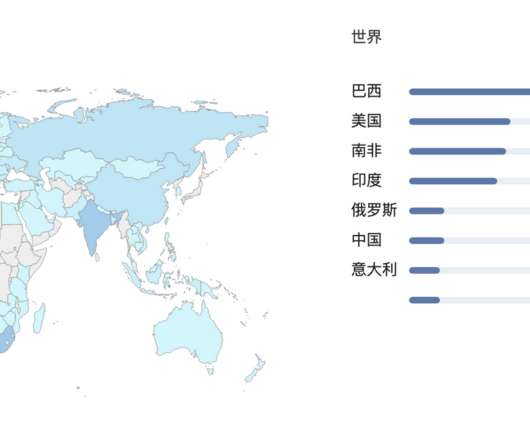
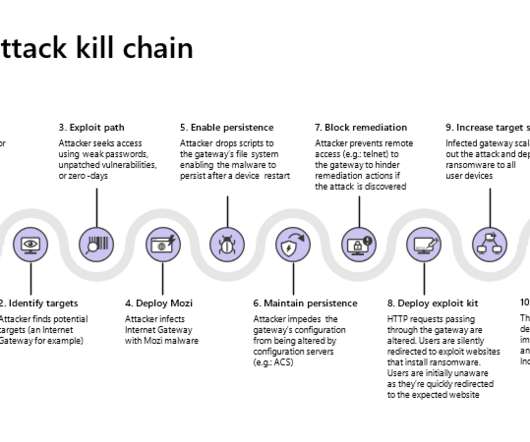
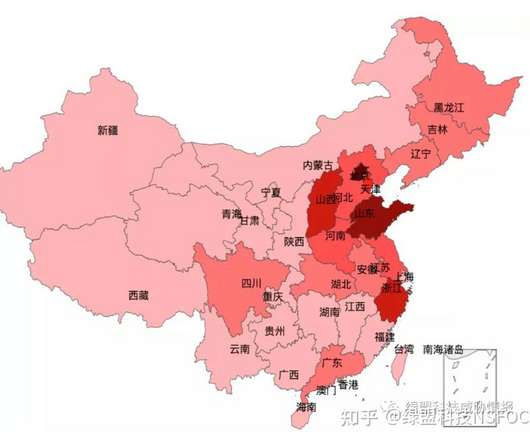
Unauthenticated RCE can allow hacking DrayTek Vigor routers without user interaction
Security Affairs
AUGUST 4, 2022
All the affected models have a patched firmware available for download on the vendor’s website.” SecurityAffairs – hacking, DrayTek Vigor). The post Unauthenticated RCE can allow hacking DrayTek Vigor routers without user interaction appeared first on Security Affairs. Pierluigi Paganini.










Let's personalize your content