The Growing Presence (and Security Risks) of IoT
Thales Cloud Protection & Licensing
NOVEMBER 6, 2019
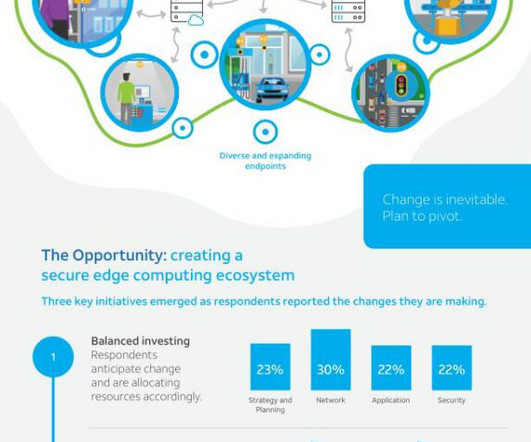
As most of us know, IoT devices are on the rise in enterprise networks. According to McKinsey & Company , the proportion of organizations that use IoT products has grown from 13 percent in 2014 to 25 percent today. The issue is that these tens of billions of new devices will likely amplify the inherent security risks of IoT.












Let's personalize your content