MY TAKE: Why companies and consumers must collaborate to stop the plundering of IoT systems
The Last Watchdog
NOVEMBER 9, 2020
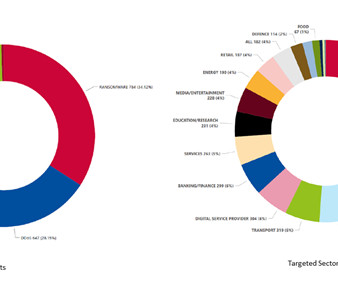
The Internet of Things (IoT) has come a long, long way since precocious students at Carnegie Melon University installed micro-switches inside of a Coca-Cola vending machine so they could remotely check on the temperature and availability of their favorite beverages. Related: Companies sustain damage from IoT attacks That was back in 1982.


















Let's personalize your content