Phish of GoDaddy Employee Jeopardized Escrow.com, Among Others
Krebs on Security
MARCH 31, 2020
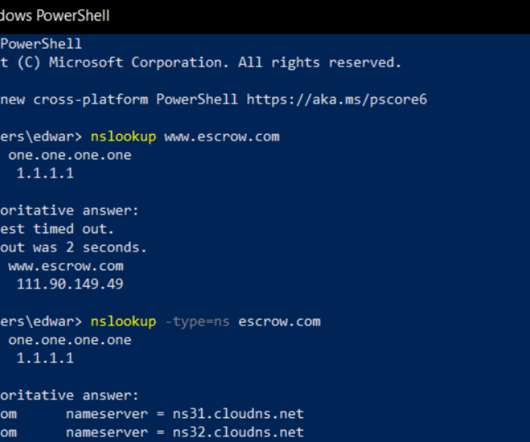
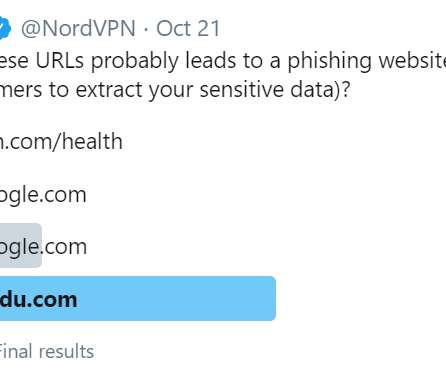
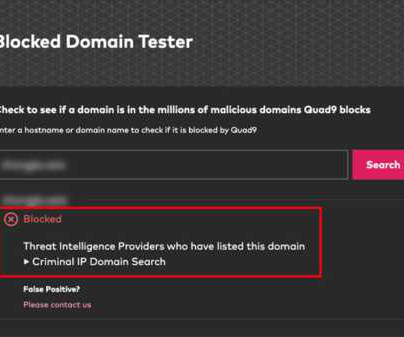
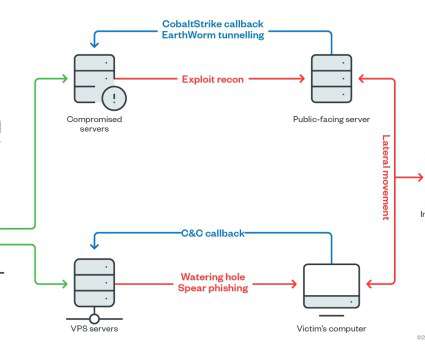
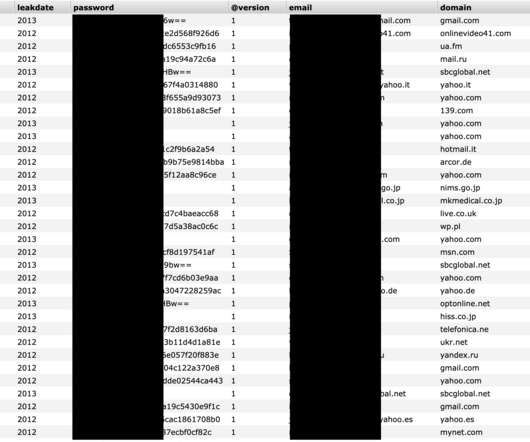
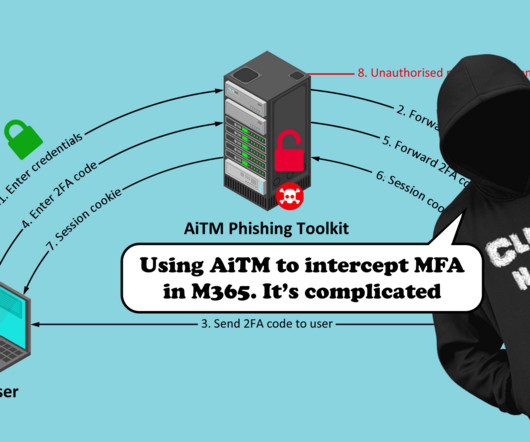
A spear-phishing attack this week hooked a customer service employee at GoDaddy.com , the world’s largest domain name registrar, KrebsOnSecurity has learned. 49 (that domain is hobbled here because it is currently flagged as hosting a phishing site). Running a reverse DNS lookup on this 111.90.149[.]49 Image: Escrow.com.




































Let's personalize your content