Protect Your Business With This Seamless Firewall — Now $150 Off
Tech Republic Security
MARCH 27, 2024
DNS FireWall is an intuitive security app built to protect you and your business from malware, phishing, botnets and more security threats.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

eSecurity Planet
FEBRUARY 14, 2024
Stateful inspection is a firewall feature that filters data packets based on the context of previous data packets. This important feature uses header information from established communication connections to improve overall security. Table of Contents Toggle How Does Stateful Inspection Work? Stateless protocols (UDP, HTTP, etc.)
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
NOVEMBER 10, 2023
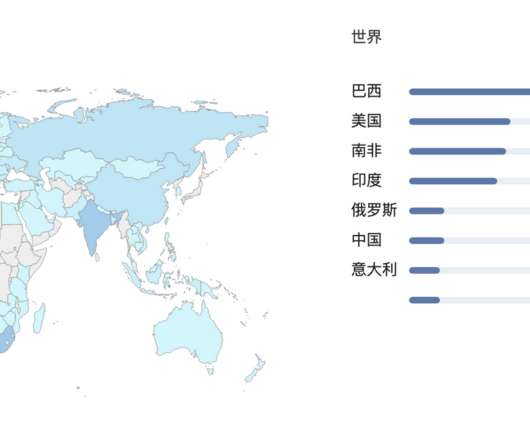
DNS security protects the domain name system (DNS) from attackers seeking to reroute traffic to malicious sites. Since a majority of business IT traffic now accesses or passes through the internet, DNS plays an increasingly important — and vulnerable — role.

eSecurity Planet
JANUARY 5, 2024
A firewall policy is a set of rules and standards designed to control network traffic between an organization’s internal network and the internet. It aims to prevent unauthorized access, manage data movement, and guard against potential security threats.
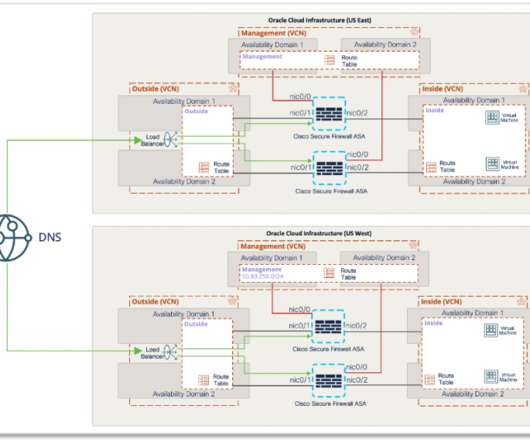
Cisco Security
JULY 9, 2021
With Cisco Secure Firewall, organizations are able to build a scalable RAVPN architecture on OCI, providing employees secure remote access to their organization’s resources from any location or endpoint. It enforces security at the DNS layer to block malware, phishing, and command and control callbacks over any port.

SC Magazine
MARCH 4, 2021
The National Security Agency (NSA) and Cybersecurity and Infrastructure Agency (CISA) released a joint information sheet Thursday that offers guidance on the benefits of using a Protective Domain Name System (PDNS). A PDNS service uses existing DNS protocols and architecture to analyze DNS queries and mitigate threats.
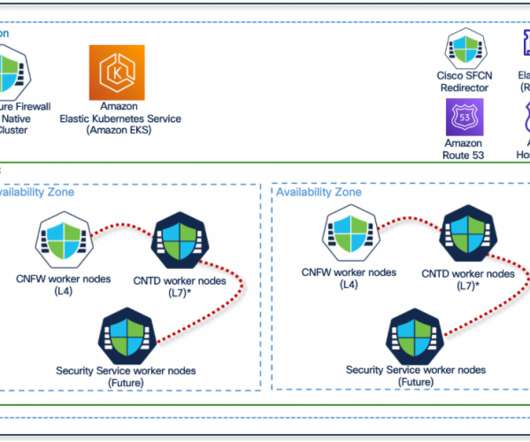
Cisco Security
MAY 26, 2021
This is where Cisco Secure Firewall Cloud Native (SFCN) comes in. It gives you the flexibility to provision, run, and scale containerized security services. Figure 1 – Cisco Secure Firewall Cloud Native platform overview. Figure 2 – Cisco Secure Firewall Cloud Native platform components.
Webroot
FEBRUARY 16, 2021
In recent months, you’ve likely heard about DNS over HTTPS , also known as DNS 2.0 and DoH, which is a method that uses the HTTPS protocol to encrypt DNS requests, shielding their contents from malicious actors and others who might misuse such information. Ultimately, this DNS privacy upgrade has been a long time coming.

CyberSecurity Insiders
MAY 18, 2022
But what are your options for proactive protection when the notion of a walled-in network has been shattered by the proliferation of new IoT devices, growth of cloud services, and new hybrid work from home models? So why aren’t more organizations taking advantage of protective DNS? So where do we go from here?
Webroot
MARCH 29, 2021
A firewall with the right threat intelligence embedded could have blocked communications with the command-and-control server thus preventing a Trojanized Orion install from connecting back to the attackers and stopping them from furthering the attack. Outside of the corporate firewall, it is the Wild West.

SC Magazine
MARCH 31, 2021
Centripetal Networks filed a lawsuit this month accusing Palo Alto of violating 12 separate patents for systems or policies designed to enhance network security. Worth noting that Centripetal has pursued – and won – patent cases against other industry titans in the past for incorporating its security innovations.

Webroot
MARCH 9, 2021
DNS (Domain Name System) is especially vulnerable. One of the most common methods of infiltration includes internet-based attacks, such as Denial of Service (DoS), Distributed Denial of Service (DDoS) and DNS poisoning. However, cybercriminals can also use legal DNS traffic surveillance to their advantage.

Webroot
MAY 26, 2021
Remote workers were abruptly pulled out from behind the corporate firewall, immediately becoming more susceptible to the targeted attacks of cybercriminals. Many office workers have yet to return to the office in the volumes they worked in pre-pandemic. For MSPs, that makes up a good portion of their clientele.

eSecurity Planet
DECEMBER 8, 2023
Domain name service (DNS) attacks threaten every internet connection because they can deny, intercept, and hijack connections. With the internet playing an increasing role in business, securing DNS plays a critical role in both operations and security. Everything You Need to Know.

The Last Watchdog
DECEMBER 13, 2020
The problem here is that a secured, cost-effective, and efficient networkmust be developed to support remote operations at scale. Many enterprises have accelerated their use of Virtual Private Network (VPN) solutions to support remote workers during this pandemic. The makeup of SASE . But it much further.
Security Affairs
OCTOBER 5, 2020
Security researchers provided technical details about an IoT botnet dubbed Ttint that has been exploiting two zero-days in Tenda routers. Security researchers at Netlab, the network security division Qihoo 360, have published a report that details an IoT botnet dubbed Ttint.

CyberSecurity Insiders
MARCH 21, 2021
When it comes to protecting your small business from cyber attacks, the first and foremost thing is to upgrade your network security and IT infrastructure to the latest standards. Modern technology comes with improved network security offering higher protection. . Build a cyber security plan . Firewalls .

eSecurity Planet
JULY 25, 2022
The domain name system (DNS) is basically a directory of addresses for the internet. Your browser uses DNS to find the IP for a specific service. For example, when you enter esecurityplanet.com, the browser queries a DNS service to reach the matching servers, but it’s also used when you send an email. DNS spoofing or poisoning.

SC Magazine
MAY 5, 2021
Signage with logo at the Silicon Valley headquarters of computer security and firewall company Palo Alto Networks, Santa Clara, California, August 17, 2017. Palo Alto Networks asked a Virginia judge to dismiss a patent lawsuit filed against them by Centripetal Networks.

Cisco Security
MARCH 17, 2021
For organizations with large footprint of remote employees, zero trust network access (ZTNA) prevents unauthorized access, contains breaches, and limits an attacker’s lateral movement on your network.

eSecurity Planet
MARCH 14, 2023
Network security creates shielded, monitored, and secure communications between users and assets. Securing the expanding, sprawling, and sometimes conflicting collection of technologies that make up network security provides constant challenges for security professionals.
Cisco Security
AUGUST 11, 2021
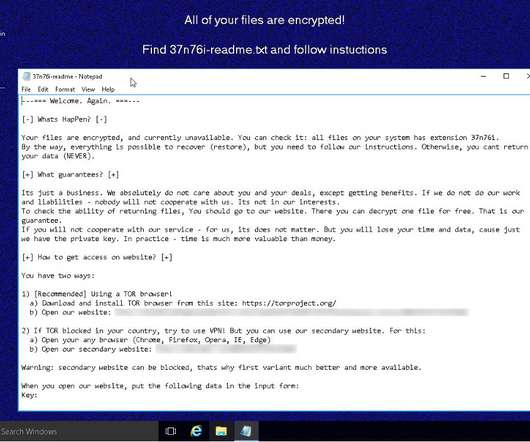
We looked at REvil, also known as Sodinokibi or Sodin, earlier in the year in a Threat Trends blog on DNS Security. In it we talked about how REvil/Sodinokibi compromised far more endpoints than Ryuk, but had far less DNS communication. Figure 1-DNS activity surrounding REvil/Sodinokibi. Changing firewall rules.

eSecurity Planet
JULY 7, 2023
Popular DDoS Web Analytics Tools Some popular DDoS web analytics tools include: CloudFlare Web Application Firewall Sucuri Website Firewall Azure Web Application Firewall AWS WAF Imperva Early Warning Signs of a DDoS Attack Having tools like web application firewalls and monitoring services in place are your best defense against a DDoS attack.

SiteLock
AUGUST 27, 2021
With cyberthreats increasing in variety, protecting your website is no longer about installing a basic firewall. You also need to consider the necessary add-ons in all the right places to develop a multi-layered security plan. Add-Ons That Help Website Security. CDN Deployment.

Cisco Security
JUNE 15, 2021
As a network and workload security strategy leader, I spend a lot of time thinking about the future of the good old network firewall. Spoiler alert: I’m not going to join the cool club of pronouncing the firewall dead. Insert Your Firewall Here. How this insertion happens is changing quite rapidly, though.

eSecurity Planet
MARCH 16, 2023
Network security threats weaken the defenses of an enterprise network, endangering proprietary data, critical applications, and the entire IT infrastructure. This guide to major network security threats covers detection methods as well as mitigation strategies for your organization to follow.

eSecurity Planet
MARCH 15, 2021
Ten years after the conceptual roots of zero trust, the cybersecurity industry has four methods for implementing microsegmentation: network fabric, hypervisor, agent, or NFGWs. While all four approaches can help your organization move towards microsegmentation, some are critical to comprehensive network security. .

eSecurity Planet
MAY 25, 2022
An ideal security stack provides continuous protection without gaps. IDS and IPS solutions help fill in the gaps between endpoint protection , firewalls , and other parts of the security stack. Why We Still Need Network Detection and Protection. Also read: Best Network Monitoring Tools.

eSecurity Planet
SEPTEMBER 24, 2021
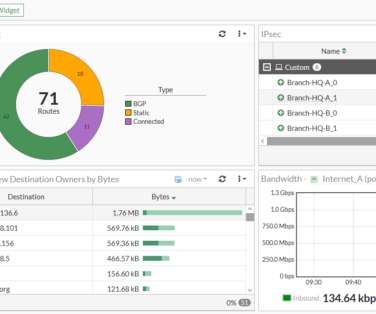
InsightIDR comes with several dashboard views that give administrators visibility into network activity like firewall traffic, blocked traffic by port and IP, total DNS traffic, and DNS queries. Alert Logic AT&T Cybersecurity BeyondTrust Crowdstrike F-Secure Invicti LogRhythm. Rapid7 Competitors.

The Last Watchdog
MARCH 26, 2020
Related: Why cybersecurity should reflect societal values An emerging approach, called Network Traffic Analysis , is gaining traction as, in effect, a catch-all network security framework positioned at the highest layer of the networking stack. Just ask Equifax or Capital One.

eSecurity Planet
FEBRUARY 23, 2024
An application gateway, also known as an application level gateway (ALG), functions as a critical firewall proxy for network security. Its filtering capability ensures that only certain network application data is transmitted, which has an impact on the security of protocols including FTP, Telnet, RTSP, and BitTorrent.

eSecurity Planet
SEPTEMBER 3, 2022
For example, the 2016 DDoS attack on the Dyn managed domain name service (DNS) caused the DNS service to fail to respond to legitimate DNS inquiries and effectively shut down major sites such as PayPal, Spotify, Twitter, Yelp, and many others. Also read: How to Secure DNS. Types of DDoS Attacks.

eSecurity Planet
JUNE 21, 2022
SSCP (Systems Security Certified Practitioner). SSCP from (ISC)2 is a mid-level certification designed for IT administrators, managers, directors, and network security professionals responsible for the hands-on operational security of their organization’s critical assets. As of mid-2022, the cost is $381 USD.

Pen Test Partners
SEPTEMBER 13, 2023
Section 6 A requirement coming into force in March 2025 is that organisations will need to have a web application firewall in place for any web applications exposed to the internet. IDS/IPS solutions must detect and alert on any covert malware communications being used such as DNS tunnelling.
eSecurity Planet
DECEMBER 2, 2021
A next-generation firewall (NGFW) is an important component of network security and represents the third generation of firewall technology. To add to the stateful inspection of network traffic and access control , NGFWs can block modern, sophisticated threats like application-layer attacks and advanced malware.

eSecurity Planet
MARCH 22, 2023
Networks connect devices to each other so that users can access assets such as applications, data, or even other networks such as the internet. Network security protects and monitors the links and the communications within the network using a combination of hardware, software, and enforced policies.
eSecurity Planet
APRIL 14, 2023
Cloudflare’s bot management solution is integrated with its Content Delivery Network (CDN) and web application firewall , which allows for more comprehensive protection against bot attacks. Cloudflare offers a range of security and performance solutions, including DDoS protection and website optimization.

McAfee
DECEMBER 1, 2021
CVE-2021-20322: Of all the words of mice and men, the saddest are, “it was DNS again.” Palo Alto Networks (PAN) firewalls that use its GlobalProtect Portal VPN running PAN-OS versions older than 8.1.17 Next, call up whoever manages your firewall and demand they power it down immediately – use threats if you must.

eSecurity Planet
JUNE 8, 2023
It is very affordable for an organization to enable their security tools and web servers to check for and enforce these protocols. It can be time consuming to establish these protocols on an organization’s DNS servers, but doing so will provide two key benefits.
eSecurity Planet
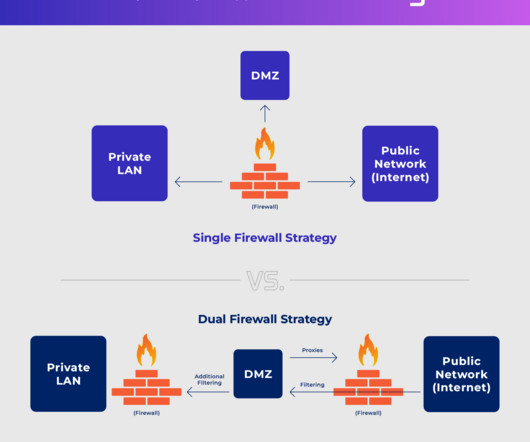
APRIL 7, 2023
A DMZ network, or a demilitarized zone, is a subnetwork in an enterprise networking environment that contains public-facing resources — such as web servers for company websites — in order to isolate them from an enterprise’s private local area network (LAN).

McAfee
DECEMBER 22, 2021
Ensure you run configuration audits for cloud assets that allow unrestricted outbound access and does not use firewalls or NAT GW’s for outbound connections. Network Security Platform. identify outbound communication attempts to known C2 domains through DNS or Web traffic.

eSecurity Planet
NOVEMBER 3, 2022
For effective DDoS defense, priority for patching and updates should be placed on devices between the most valuable resources and the internet such as firewalls, gateways , websites, and applications. Hardening includes, but is not limited to: Block unused ports on servers and firewalls. Anti-DDoS Architecture. Anti-DDoS Tools.

eSecurity Planet
AUGUST 23, 2023
In order to verify the signature, the recipient’s email server will then use the sender’s publicly available key that is provided in DNS records for this domain. Endpoint security tools like EDR typically include security software capable of detecting and blocking dangerous attachments, links, and downloads.

eSecurity Planet
SEPTEMBER 25, 2023
The lowest tier of Cloudflare One provides support for 50 users maximum, 24 hours of activity logging, and up to three network locations for office-based DNS filtering. Upgrading to the pay-as-you-go tier eliminates any user maximum and provides 30 days of activity logging and 20 office-based DNS filtering network locations.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content