BlackLotus Malware Hijacks Windows Secure Boot Process
Schneier on Security
MARCH 8, 2023
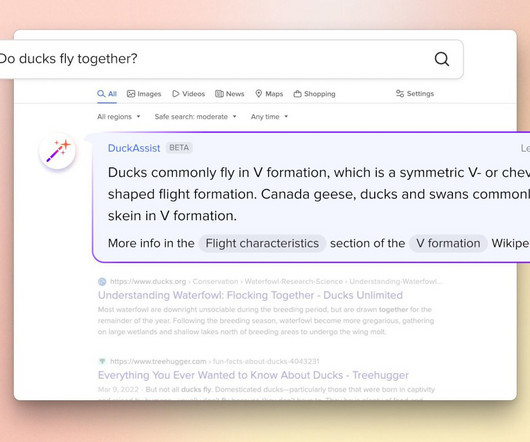
Researchers have discovered malware that “can hijack a computer’s boot process even when Secure Boot and other advanced protections are enabled and running on fully updated versions of Windows.” Dubbed BlackLotus, the malware is what’s known as a UEFI bootkit. These sophisticated pieces of malware target the UEFI—short for Unified Extensible Firmware Interface —the low-level and complex chain of firmware responsible for booting up virtually every modern computer.







































Let's personalize your content