QBot malware abuses Windows WordPad EXE to infect devices
Bleeping Computer
MAY 27, 2023
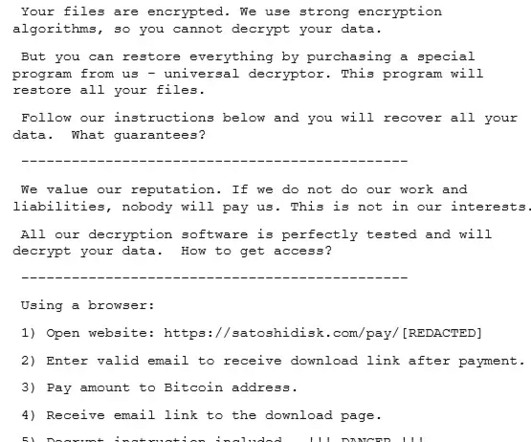
The QBot malware operation has started to abuse a DLL hijacking flaw in the Windows 10 WordPad program to infect computers, using the legitimate program to evade detection by security software. [.















Let's personalize your content