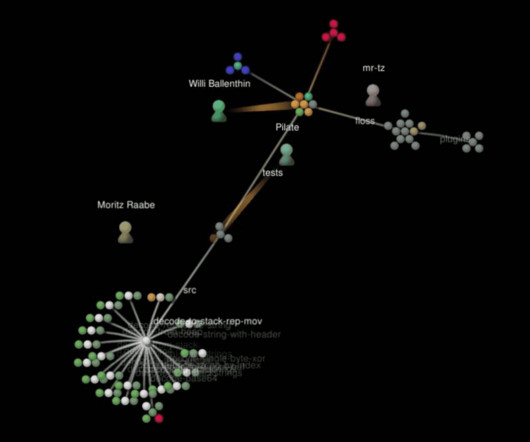
Exposing the inner-workings of the ransomware economy
Elie
SEPTEMBER 8, 2017
This blog post shed light on the inner workings of the ransomsphere economics and exposes which cybercriminal groups are the biggest earners. This is the second blog post in my series about ransomware economics. The first post. is dedicated to the methodology and techniques needed to trace ransomware payments end-to-end. As this post builds on that methodology, I encourage you to read through the first post if you haven’t done so.



















Let's personalize your content