Ransomware Cheat Sheet: Everything You Need To Know In 2024
Tech Republic Security
JUNE 27, 2024
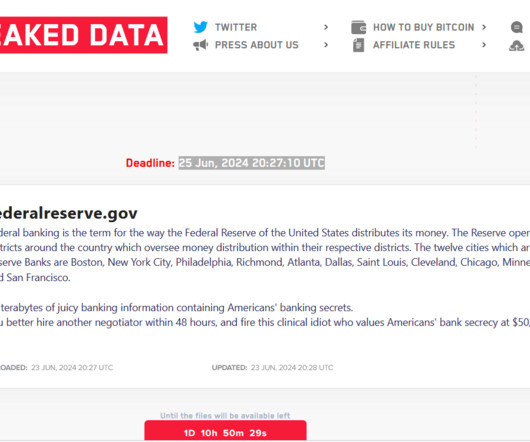
This guide covers various ransomware attacks, including Colonial Pipeline, WannaCry and LockBit, the systems hackers target and how to avoid becoming a victim and paying cybercriminals a ransom.






























Let's personalize your content