Protecting Oil and Gas Industry Infrastructure: Strategies for Resilience
SecureWorld News
JANUARY 16, 2025
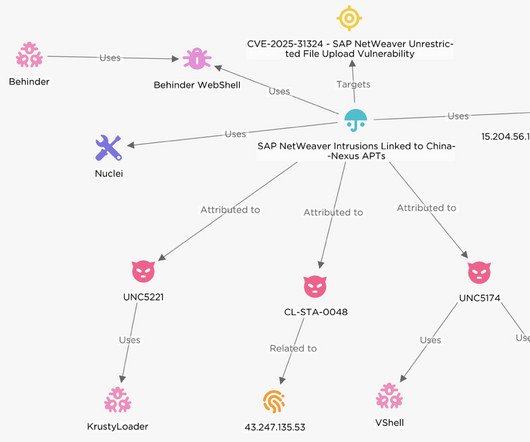
To ensure energy security and economic stability, protecting the infrastructure is essential. A report from 2023 revealed that 67% of energy and utility companies faced ransomware attacks, with many incidents exploiting unpatched vulnerabilities. Incident response plans: Organizations should have tested recovery plans in place.

















Let's personalize your content