Thales 2023 Data Threat Report: Sovereignty, Transformation, and Global Challenges
Thales Cloud Protection & Licensing
MAY 8, 2023
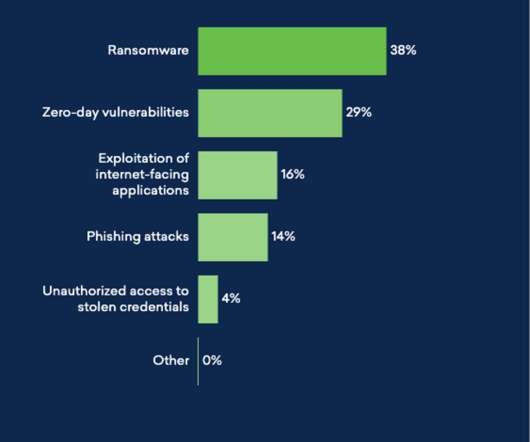
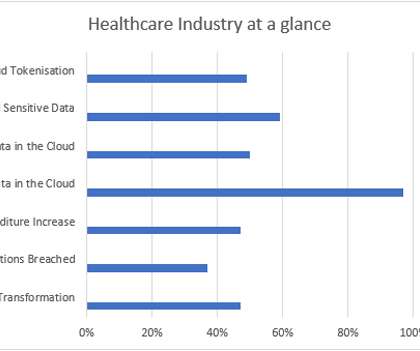
Thales 2023 Data Threat Report: Sovereignty, Transformation, and Global Challenges madhav Tue, 05/09/2023 - 05:30 Despite the economic and geopolitical instability in 2022, enterprises continued to invest in their operations and digital transformation. This article highlights the key findings of the report.












































Let's personalize your content