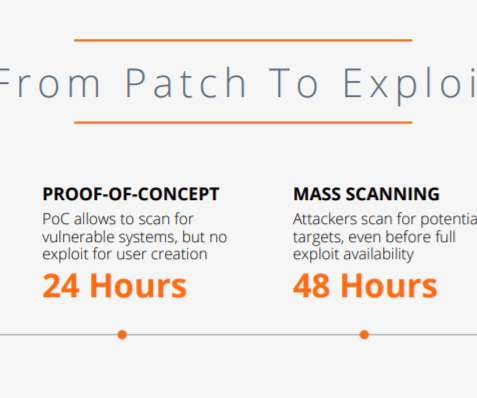
SAP systems are targeted within 72 hours after updates are released
Security Affairs
APRIL 6, 2021
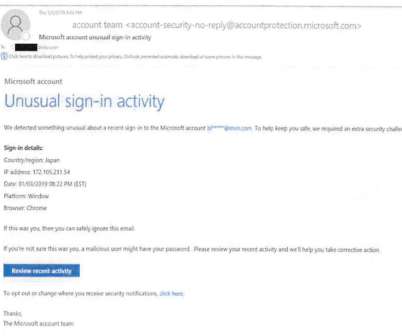
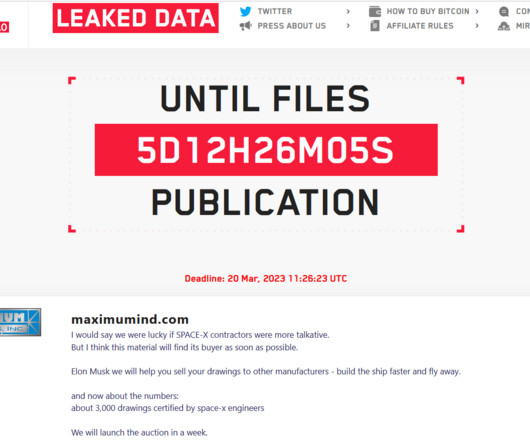
Furthermore, attackers used proof-of-concept code to attack SAP systems, but also brute-force attacks to take over high-privileged SAP user accounts. The goal of these attacks was to take full control of an SAP deployment in order to modify configurations and user accounts to exfiltrate business information.















Let's personalize your content