ISaPWN – research on the security of ISaGRAF Runtime
SecureList
MAY 23, 2022
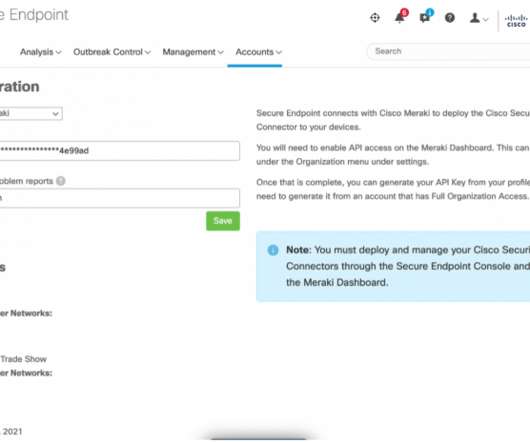
This report includes an analysis of the ISaGRAF framework, its architecture, the IXL and SNCP protocols that are used to program and control ISaGRAF-based devices and to communicate with them. Since authentication data is encrypted with a preset symmetric key, the attacker could decrypt an intercepted target (device) password.
















Let's personalize your content