Experts linked ransomware attacks to China-linked APT27
Security Affairs
JANUARY 4, 2021
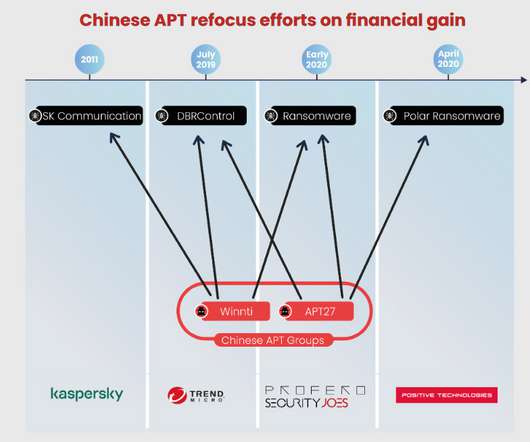
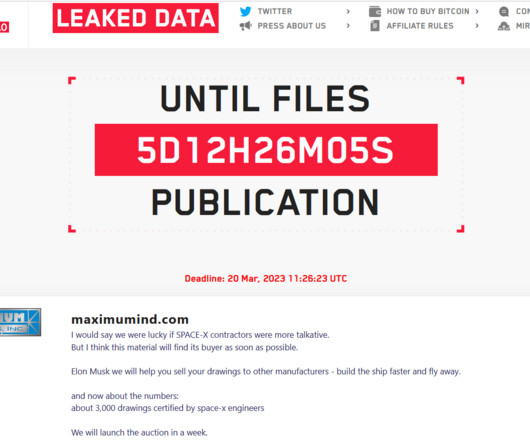
Researchers from security firms Profero and Security Joes linked a series of ransomware attacks to the China-linked APT27 group. Security researchers from security firms Profero and Security Joes investigated a series of ransomware attacks against multiple organizations and linked them to China-linked APT groups.

























Let's personalize your content