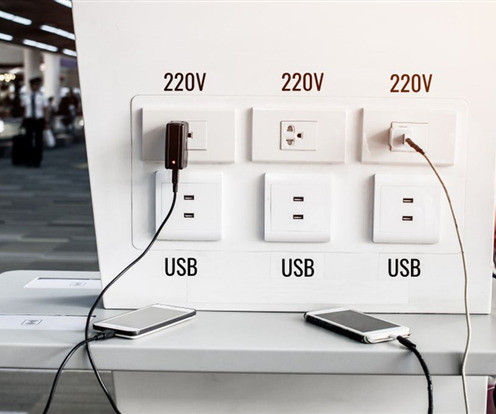
Don't plug your phone into a free charging station, warns FBI
Malwarebytes
APRIL 11, 2023
The term was first used by Brian Krebs in 2011 after a proof of concept was conducted at DEF CON by Wall of Sheep. There are many categories of malware that cybercriminals could install through juice jacking, including adware, cryptominers, ransomware, spyware, or Trojans.










Let's personalize your content