Will cryptocurrency mining soon saturate AWS, Microsoft Azure and Google Cloud?
The Last Watchdog
JUNE 20, 2018
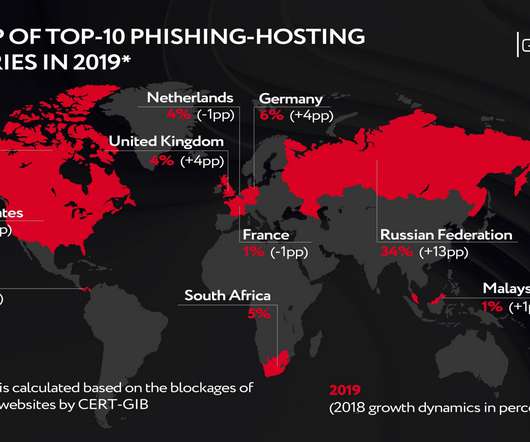
Cryptojacking, as defined by the Federal Trade Commission , is the use of JavaScript code to capture cryptocurrencies in users’ browsers without asking permission. LW: So cryptocurrency got discovered as the ideal payment vehicle for ransomware. In 2011, total cryptocurrency value was about $10 billion. Bilogorskiy.

















Let's personalize your content