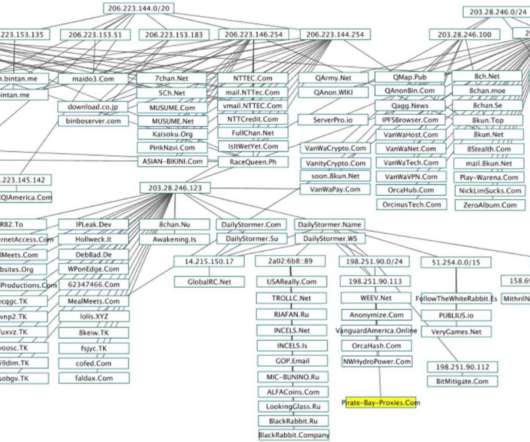
The Now-Defunct Firms Behind 8chan, QAnon
Krebs on Security
OCTOBER 22, 2020
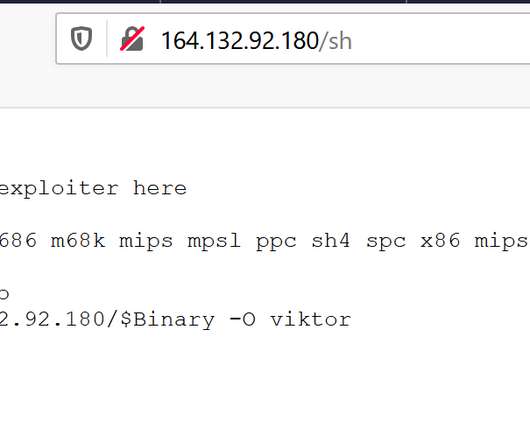
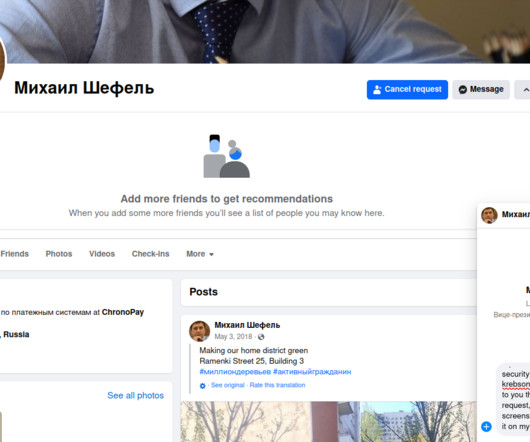
Some of the world’s largest Internet firms have taken steps to crack down on disinformation spread by QAnon conspiracy theorists and the hate-filled anonymous message board 8chan. based Internet Service Provider that serves as N.T. Technology’s colocation provider and sole connection to the larger Internet.


















Let's personalize your content