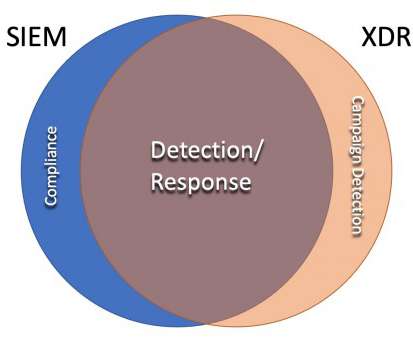
SOC 2025: Detection/Analytics
Security Boulevard
MARCH 10, 2022
Once you have internal and external data collected and aggregated, you analyze the data to identify the attacks. Then they mine security data to find and follow an attacker’s trail to identify what the attackers have done and project what they’ll do next. Easy, right? Mike Rothman. (0) 0) Comments.


















Let's personalize your content